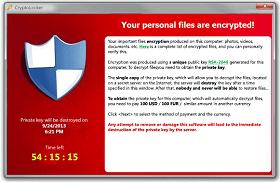
Ransomware, such as the Locky Virus and CryptoLocker Virus, or WannaCry are quite prevalent in the news today. It continues to be one of the most talked about security issues plaguing businesses around the globe. If your business uses email or is connected to the internet, then you are susceptible to infection. These viruses, are typically distributed via malicious file(s) sent to you and your employees via email, often disguised as your everyday Microsoft Word (.doc) files. When they arrive in email form, they should of course be considered spam messages, however often times they evade capture by even the best spam filtering mechanisms on the market; as they are often cleverly crafted by hackers using newly formed techniques. Once you or your employee receives the email message and lets their curiosity get the best of them, they may open the attached file, then, unfortunately, it’s too late; the virus goes to work infecting their workstation and eventually in most cases your offices network file server. Unfortunately, once this occurs, the virus will encrypt the files on your network, rendering them useless and unreadable. Unless, of course, you have the decryption mechanism – which, newsflash, you dont! You will likely spend the next several hours, frantically calling for help, attempting to remove the malware from your network. You will also more than likely be greeted with a not so friendly message on your computer screen (like the one shown below),
informing you, that in order to decrypt the files and eradicate the virus, you must contact ‘some company‘ (aka the perpetrators of the virus) via phone or email and they will ask for a fee (usually payable via BitCoin or some other cryptocurrency) in order to decrypt the files for you; thus holding you and your business hostage.
One way that a business can best prepare for such a malicious attack, is to implement a formidable backup solution and more importantly test that backup for validity often. A worthy backup solution, is the kind that implements a real time continuous backup methodology; allowing you to restore your server(s) or file(s) to a specific point in time- like a snapshot. Although this may not seem like the most elegant solution in fighting against ransomware, it does make the “Top 10” list. Let’s face it, your business needs backup, so why not get the most capable one available?
Datto SIRIS 3 is one such backup utility – Contact Us to learn more about how leveraging Datto backup technology can help your business when disaster strikes.
With this type of backup mechanism in place, you can simply ‘roll back’ to a previous point in time (before the infection occurred of course) and restore file(s) or your entire server to that ‘clean/ransomware-free’ point in time. Having this option at your disposal, can be a real lifesaver in the event your business faces such a crisis. This type of backup also provides you real disaster recovery & business continuity options as well.
So, what else can be done to protect my business against such malicious attacks?
Well, Technation knows how… we start by performing a FREE security audit of your business, much like a security penetration test of your office network and its perimeter. We discover ‘what’s out there’, then we look for vulnerabilities (just like an attacker does) in each of your assets and provide recommendations for remediation. Almost 100% of the time, a company’s office network is wide open, put in simple terms; most areas are susceptible to easy attack. It’s all about closing the attack-surface.
Most networks have so many moving pieces, that no one tool can provide total protection. Instead, much like a Swiss army knife, it’s all about -using the right tool for the job. Following this initial discovery phase, Technation will begin an in depth decision making phase in order to determine how to appropriately protect each of your businesses assets. This decision process, also known as the recommended remediation phase, should not be taken lightly. There is nothing worse than buying things you don’t need or things which won’t necessarily work for a given scenario. Unfortunately, deciphering this is not a skill most IT geeks possess. Therefore, if you are a business owner, we hope you agree, that there is a huge difference between maintenance and prevention. Anyone is capable of becoming an expert on the IT tools & infrastructure in front of them on a daily bases, I mean, sure, things are working, the server is up, things seem to be fine, etc, but are they thinking outside the box, or just seeing & maintaining the same old stuff? Additionally, are they recommending new technologies, and in turn protecting your business & saving you money? Or, is ignorance bliss?